Overview:
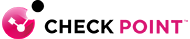
Web access is a predominant route for attacks on enterprises. Check Point URL Filtering controls access to millions of web sites by category, users, groups, and machines to protect users from malicious sites and enable safe use of the Internet. URL Filtering employs UserCheck technology, which educates users on web usage policy in real time.

Secure
Protects users with cloud-based categorization and UserCheck technology

Efficient
Enable on any Check Point security gateway reducing Total Cost of Ownership

Unified
Unified security across all aspects of the web with full Application Control integration

Benefits:
Protect users with cloud-based categorization and UserCheck technology
- Dynamic cloud-based database of over 100,000,000 Websites
- Real time updates of ever evolving and new URLs
- Leverage UserCheck to empower users with real time alerts while educating on web policy
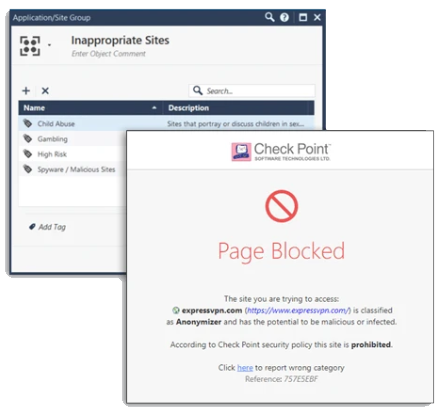
Fully integrated with Application Control for complete secure web usage
- Allow unified enforcement and management across all aspects of web security
- Define, enforce and report on web and application security policies at the user and group levels
- Control over 100 Million websites, 4,500 Web 2.0 applications, and 225,000 widgets to achieve the highest level of web security
- Enforce bandwidth and/or time limits to select websites or Web 2.0 applications
Optimize security and reduce Total Cost of Ownership
- Full integration of URL Filtering into Check Point gateways eliminates bypass through external proxies and enforces inspection of all traffic--even when traversing non-standard ports
- Scan and secure SSL encrypted traffic passing through the gateway
- Easy one click activation leveraging the Software Blade Architecture
- Up to 90% reduction of TCO compared to traditional point solution
Features:
Extensive and Dynamic URL Coverage
URL Filtering provides organizations with the ability to dynamically allow, block or limit access to certain websites in real-time. URL Filtering can control access to entire websites or just pages within a website, with fine-tuning policies incorporated to white list and black list specific URLs.
Inspects SSL/TLS Encrypted Traffic
HTTPS inspection scans and secures SSL encrypted traffic passing through the gateway. Gateways using HTTPS inspection decrypt the traffic with the sender's public key, inspect and protect, then re-encrypt the content to send back to the sender. Encrypted content passing through a gateway that should not be inspected can be bypassed with a simple administrator policy definition.
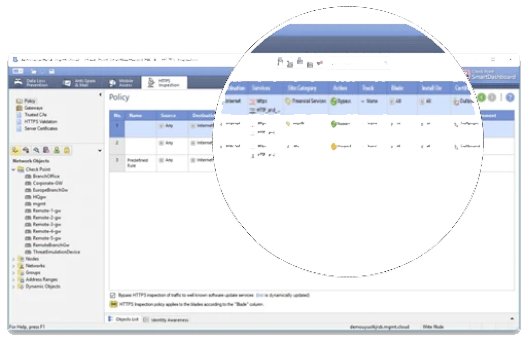
360 Degree Visibility and Reporting
Achieve an unmatched level of visibility to detect web access security events and prevent them. Check Point URL Filtering seamlessly integrates with SmartEvent, enabling Check Point to prevent web access related security events rather than just detecting them or simply missing them.
Engines for KNOWN threats
Intrusion Prevention, Anti-bot, Anti-virus, URL Filtering, URL Reputation, IP Reputation, Domain Repulation, Anti-phishing, Identity Awareness, DDoS
Engines for UNKNOWN threats
CPU-level Inspection, Malware DNA, Threat Emulation, Threat Extraction (CDR), Campaign Hunting (AI), Context Aware Detection (AI), Huntress (AI), Zero-phishing, Anti-ransomware, Account Takeover, Malware Evasion Resistance
Integrated into the Check Point Infinty Architecture
URL Filtering is integrated into the Check Point Infintiy Architecture, and can be activated easily on Check Point Security Gateways. By just enabling URL Filtering inside their existing Check Point gateways, organizations can save up to 90% compared to traditional stand-alone URL Filtering solutions.

Specifications:
| Supported Appliance Families |
- Check Point 2200, 4000, 12000, 21400 and 61000 Appliances
- Check Point Power-1
- Check Point IP Appliances
- Check Point UTM-1
- Check Point IAS
|
| Supported Operating Systems |
- GAiA
- SecurePlatform
- IPSO 6.2 Disk-based
- IPSO 6.2 Flash-based
- Windows
|