July 24, 2019 By BlueAlly

By Dana Katz, Product Marketing Manager, Security Platforms
An ever-evolving IT environment and cyber-threat landscape have made legacy security infrastructures ineffective. Based on the outdated assumption that anything within the security perimeter can be trusted, they leave organizations exposed to cyber-attacks.
Across the industry, security professionals are designing and rebuilding their strategies around a Zero Trust approach, one that trusts no user, device or system, neither inside nor outside the perimeter.
Read this article, the first of our Zero Trust blog series, to learn more about the Zero Trust Security approach, the reasons for its adoption, and how you can practically implement it using Check Point Infinity.
Today, you no longer have to set foot in the office building to come to work. Advancements in technology have expanded what is now classifies as “the office,” with companies able to interface through mobile devices and cloud software regardless of where their employees are located.
However, these developments pose a cybersecurity dilemma. The security perimeter is no longer confined to the walls of an office building. Valuable business data transfers continuously between SaaS applications, IaaS, data centers, remote users, IoT devices, and more. Which means cyber-criminals have access to wider attack surfaces and more points of entry than ever before. As evidence, in 2018, 34% of cyber-attacks were perpetrated by insiders1.
To complicate matters even more, once these cyber-criminals are inside your perimeter, they seek and steal valuable and sensitive data for months before being detected. In fact, in most cases, it takes six months to detect a data breach2.
Alarmingly, most incumbent security infrastructures are generationally outdated and dangerously behind the level of attacks they must protect against. Clearly, it’s time for a new security paradigm.
The Zero Trust Security Approach: Never Trust, Always Verify!
Across the industry, security professionals are shifting to a Zero Trust Security state-of-mind: No device, user, workload or system should be trusted by default, regardless the location in which it is operating from, neither inside or outside the security perimeter.

Figure 1- The Forrester Zero Trust Extended Security Model
But Zero Trust is more than just a concept. The Zero Trust Extended Security model, introduced by Forrester analysts, offers seven key principles of implementation that organizations should focus on when moving toward a Zero Trust security model. Implementing these principles enables the adoption of a security posture of “Default Deny” where systems are hardened and isolated until a level of trust is established.
Let’s see what each of these principles means:
ZERO TRUST NETWORKS
When moving toward Zero Trust Security, it is crucial you “Divide and Rule” your network. Identifying your valuable assets and defining “Micro-segments” around them create multiple junctions and inspection points that block malicious or unauthorized lateral movement, so that in the event of a breach, the threat is easily contained and isolated.
ZERO TRUST WORKLOADS
Securing workloads, particularly those who are running in the public cloud, is essential since these cloud assets (e.g., containers, functions, and VMs) are vulnerable and attractive targets to malicious actors.
ZERO TRUST DATA
Zero Trust is all about protecting the data while it is shared continuously between workstations, mobile devices, application servers, databases, SaaS applications, and across the corporate and public networks.
ZERO TRUST PEOPLE
With 81% of data breaches involving stolen credentials2, it is clear that username and passwords no longer prove the identity of a user. Identities are easily compromised, so access control to your valuable assets must be strengthened.
ZERO TRUST DEVICES
With 70% of breaches involving compromised devices1, every device connected to your network should be treated as a threat vector, whether it’s a workstation, a mobile, or an IoT/OT device. Security teams must be able to secure every device on their network and isolate it if compromised.
VISIBILITY AND ANALYTICS
You can’t protect what you can’t see or understand. A Zero Trust Security model continually monitors, logs, correlates, and analyzes every activity across your network.
AUTOMATION AND ORCHESTRATION
A Zero Trust Security architecture must automatically integrate with the organization’s broader IT environment to enable speed and agility, improved incident response, policy accuracy, and task delegations.
Check Point Introduces Absolute Zero Trust with Check Point Infinity
However, implementing Zero Trust using disparate technologies may result in inherent security gaps and complexities. That is why Check Point now offers a holistic and practical approach to implementing Zero Trust based on Check Point Infinity, a consolidated security architecture.
Absolute Zero Trust Security is the Check Point interpretation of the Zero Trust security. Based on Check Point Infinity It offers a complete, efficient, and preventive implementation of Zero Trust security model, enabling organizations to:
- Implement all of the Zero Trust security principles: The Check Point Infinity architecture consolidates a wide range of security functions and solutions that will allow you to implement all of the Extended Zero Trust Security Model.
- Efficiently manage Zero Trust using centralized security management and a unified policy- resulting in a 50 percent reduction in security man-hours.
- Empower Zero Trust with Real-Time Threat Prevention, focusing on threat prevention and protecting against Zero-day attacks.
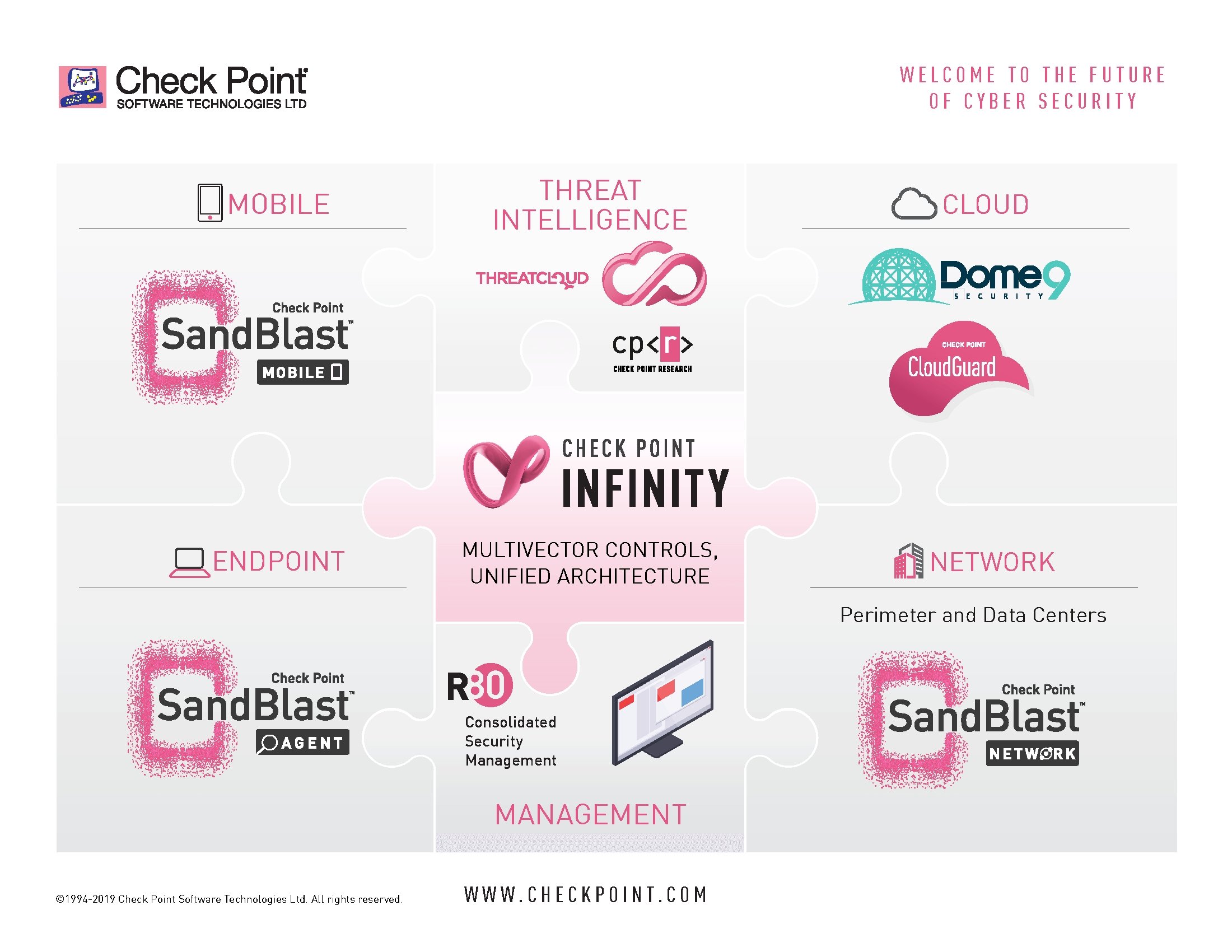
Figure 2- Check Point Infinity – A Consolidated Zero Trust Security Architecture
The Industry’s first Zero Trust Security Workshop
The concept of implementing Zero Trust may still seem foreign, but you don’t have to do it alone. Check Point can help you get there with the industry’s first Zero Trust security workshop. Here, experts will review your existing security architecture, customize a Zero Trust strategy for your business needs, create a detailed implementation plan and blueprint, and provide recommendations for operational efficiency and cost reductions.
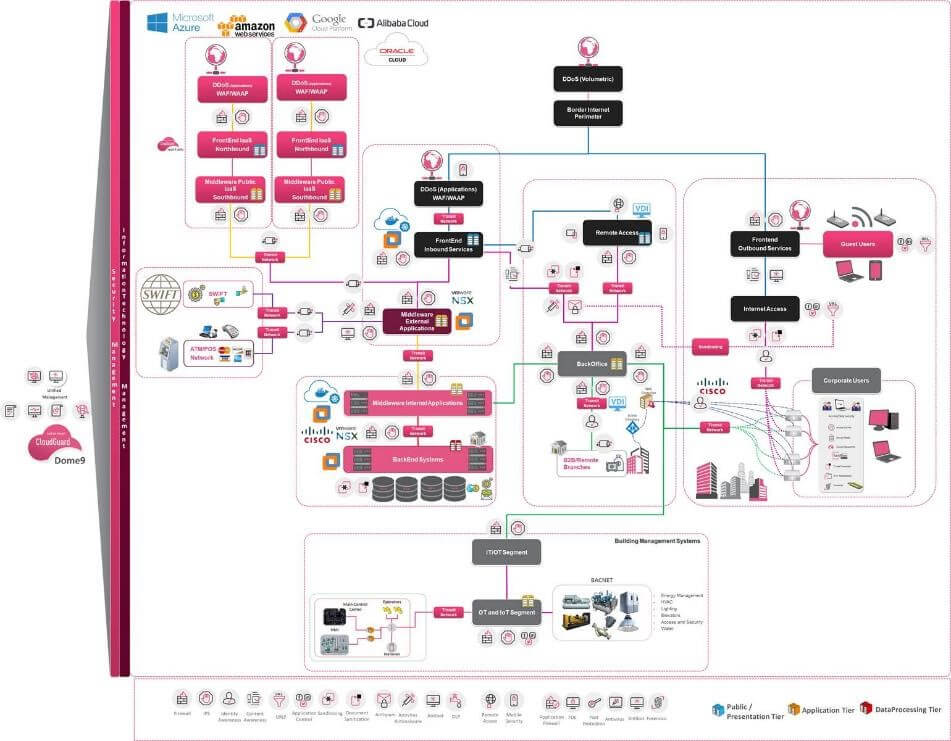
Figure 3: A Zero Trust Architecture Blueprint example designed by Check Point Security Architecture team
1Verizon DBIR 2019
2Verizon DBIR 2018
