Check Point SandBlast Agent
The Power to Protect. The Insight to Understand.
Sorry, this product is no longer available, please contact us for a replacement.
Overview:
Today’s borderless networks are redefining endpoint protection. With a variety of endpoints freely accessing networks, they’re storing sensitive corporate data. Because 70 percent of successful data breaches start on endpoints,1 a preventative approach to endpoint security can help stop cyber attacks. SandBlast Agent is the advanced endpoint protection and threat prevention solution to protect your organization.
![]()
Innovative Threat Prevention Technologies
Uses static, dynamic, and behavioral detection and prevention technologies with advanced artificial intelligence to provide high catch rates and low false positives
![]()
Insightful Detection and Response
Assures continuous collection of comprehensive and complete raw forensics data, employing full attack remediation capabilities
![]()
Complete Endpoint Security Solution
Integrates into Check Point Infinity to get maximum prevention across all attack surfaces, shared intelligence, and a single point of management (cloud service or on premise)
Product Benefits
- Simple, non - intrusive solution with intuitive user interface
- Proactively blocks new and unknown malware from reaching endpoints
- Maintains business productivity by promptly providing safe versions of downloaded files to users
- Protects user credentials by stopping phishing attacks in real - time
- Delivers a comprehensive view of attack history prior to discovery
- Drives full understanding of root cause, malware entry points, and scope of damage
- Accelerates response time and reduces chance of reinfection
Product Features
- Defends against multiple attack vectors, including web downloads, external storage devices, lateral movement, or encrypted content
- Threat Extraction reconstructs incoming files using only safe elements
- Identifies and contains infected hosts to li mit damages and malware spread
- Uses dynamic analysis and heuristics to block deceptive phishing sites
- Automatically builds actionable forensics reports with key information
- Keeps credentials safe by alerting when users attempt to utilize corporate passwords on external sites
Insights
The rise of breaches caused by sophisticated social engineering and web - based malware attacks have made web browsers a prevalent entry point for threats through endpoint devices. Malware may be hidden in web - downloaded content or webmail attachments. Your employees may unknowingly become victims of phishing and social engineering attacks. Even the simple action of employees reusing corporate credentials and passwords for non - business web services can put your organization at risk. On the other hand , users demand real - time security protections that can support their need for unconstrained access to the internet with immediate delivery of business - critical files and emails.
Additionally , with more employees using corporate devices to work remotely , and as more contractors, and consultants bring their own systems into the enterprise , cybercriminals target weaknesses in traditional endpoint security to infiltrate and in fect these workers’ systems. Once inside, hackers leverage lateral communications through the network to infect additional devices. As threats evolve, organizations must find ways to continuously detect , prevent, and respond quickly to attacks on the endpoint in order to limit damages.
So how can you keep your employees safe from these emerging threats while allowing them to work at the pace your business demands?
Solution
Check Point SandBlast Agent extends industry - leading network protections , including the advanced capabilities of SandBlast Zero - Day Protection to web browsers and endpoint devices. This ensures complete real - time coverage across threat vectors , letting your employees work safely no matter where they are without compromising on productivity. SandBlast Agent protects from threats delivered via web downloads, content copied from removable storage devices, links or attachments in email messages, lateral movement of data and malware between systems on a network segment and infections delivered via encrypted content.
Using Zero Phishing ™ technology , SandBlast Agent proactively blocks access to new and unknown deceptive sites on the web, as well as prevents the misuse of corporate passwords to safeguard user credentials.
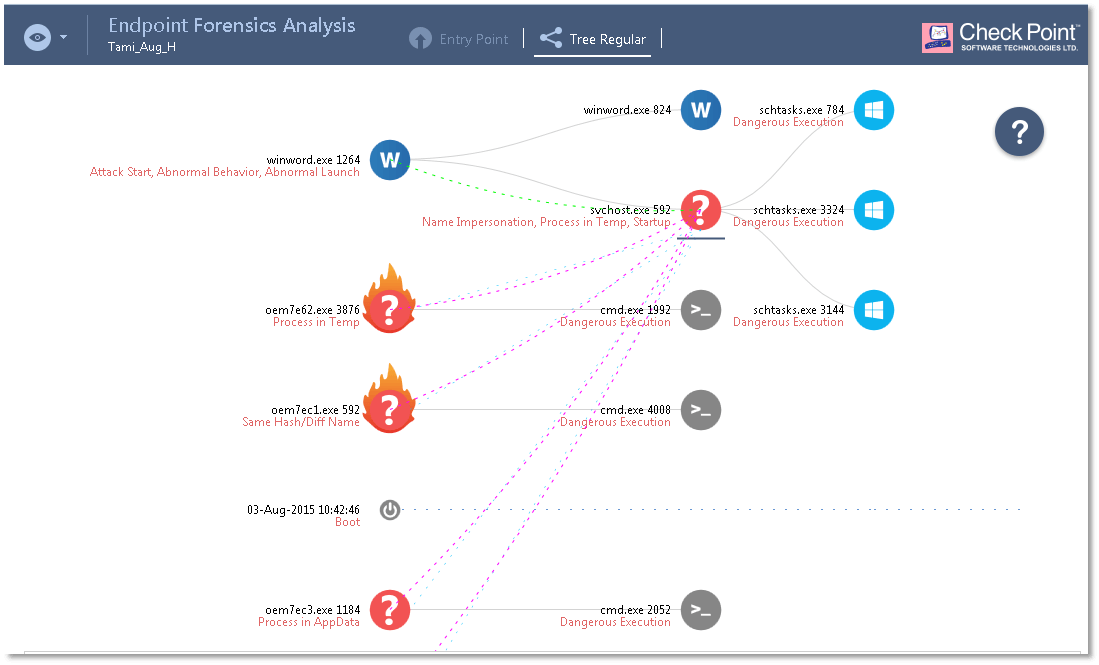
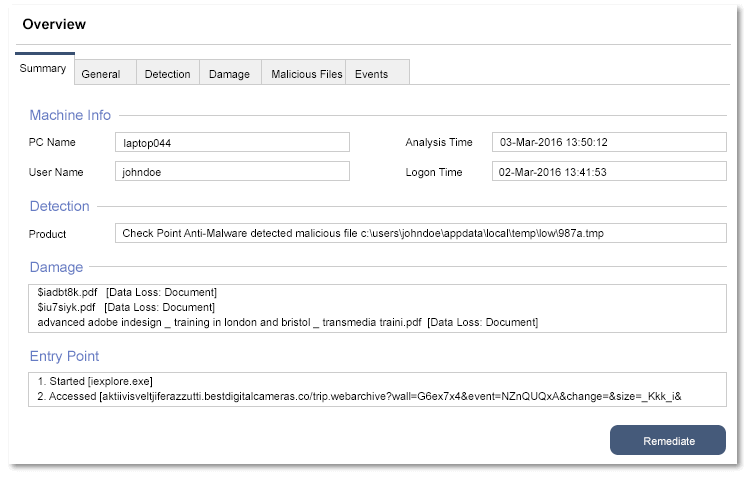
SandBlast Agent captures forensics data with continuous collection of all relevant system events, and then provides actionable incident analysis to quickly understand the complete attack lifecycle. With visibility into the scope, damage , and attack vectors, incident response teams maximize productivity and minimize organizational exposure.
Pricing Notes:
- Pricing and product availability subject to change without notice.
- These license instructions cover the following endpoint packages: Access Control, Data Protection, Anti Virus, SandBlast Agent, SandBlast Agent for Browsers, and Complete Security
- Check Point Endpoint Security, SandBlast Agent and SandBlast Agent for Browsers are licensed per protected endpoint. An Endpoint is defined as a Computer Instance in the Check Point Endpoint Security End User License Agreement
- Licensed quantities are additive per package
- Annual packages can be used only for the period of the contract
- Perpetual packages are available for the Access Control and Data Protection packages
- Each purchased package is accounted individually per the overall purchased quantity of that package
- There is no requirement for an endpoint container license
- A Threat Emulation & Extraction cloud service contract is automatically created to allow licensed SandBlast Agent installations to send files for inspection and extraction in Check Point SandBlast Cloud.
- For annual package renewal please use the annual SKU with a "-RENEWAL" suffix (e.g. CPEP-DATA-RENEWAL-1Y)
- Full Disk Encryption includes the utilization in Enterprise Workplace management mode
- Endpoint products and SandBlast Agent require Check Point Endpoint Management (EPM) for policy management. EPM is included with SmartCenter and is also available as an individual license
- SandBlast Agent for Browsers is managed from a Check Point cloud portal – a license is not required for the management
- Support for perpetual packages follows the standard rules as all Check Point perpetual software
- All endpoint annual subscription include Standard Support. The included support can be either Direct or Collaborative - based on customer region and user-center account designation. Customers may upgrade the included Standard support to either Direct Premium or Collaborative Premium support